Barnes & Noble Card-Skimming Incident: What You Can Learn
While high-profile, it's far from the first incident of its kind. Here's how you can protect your organization and members.
A favorite bookseller recently became someone’s favorite target.
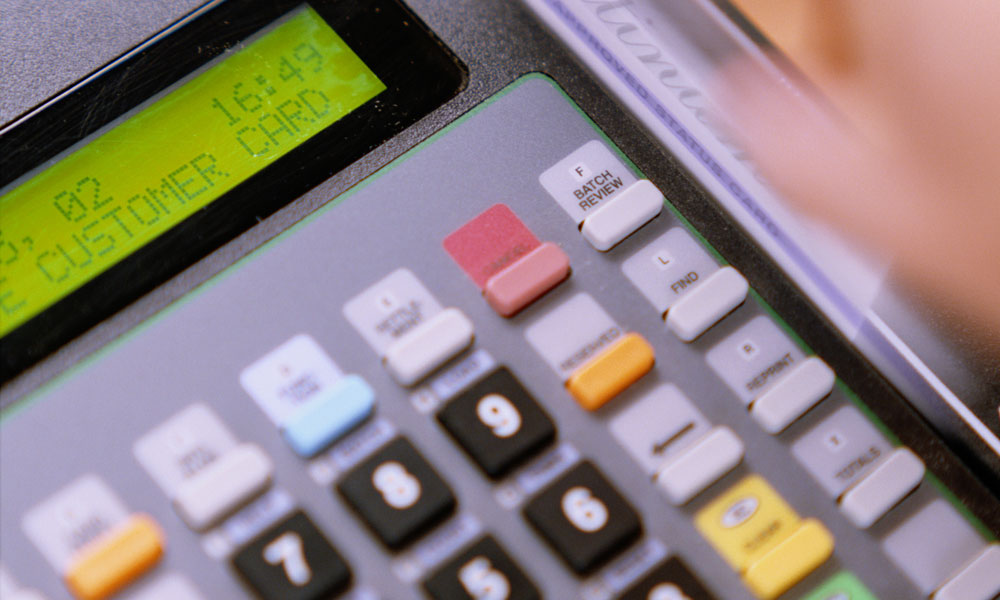
Barnes & Noble reported Tuesday night that dozens of its credit-card-scanning machines — 63 in nine states — had been tampered with, making vulnerable the information of anyone who used the affected PIN pads.
Among the major cities targeted were New York, Chicago, Miami, and San Diego. Security Week has a full list.
The incident was discovered over a month ago, but was only disclosed Tuesday. “We have acted at the direction of the U.S. government and they have specifically told us not to disclose it, and there we have complied,” an official from the company told The New York Times.
While this is perhaps the most high-profile skimming incident of its kind — in part because of the widespread, distributed nature of the attack — it’s far from the first one. Last year, for example, the craft store chain Michaels suffered a similar incident. And California’s Lucky supermarket chain also faced a similar attack.
Associations aren’t retailers, but they usually sell things. So what can you do to protect your organization and its customers?
The PCI Security Standards Council has a set of guidelines available for retailers who may be affected by such issues, along with a sheet of best practices for detecting card skimming.
“It is very important to fully understand the security implications of your terminal environment,” the guidelines state. “Where you choose to locate your terminal(s) – and everything that surrounds the terminal – has an impact on how easy it is for a criminal to compromise that terminal.”
Could this happen to your association when you transact business by credit card? What sort of security measures could be taken, at events for example, to prevent point-of-sale fraud?
(TMG archive photo)






Comments